Index
- What Is Phishing?
- Recent Trends in Phishing Affecting Businesses
- Common Phishing Practices Used by Attackers
- AlphaKOR as a Cybersecurity Solution Provider
What Is Phishing?
Definition of Phishing in Cybersecurity
Phishing represents one of the most enduring, and effective threats within modern cybersecurity, largely because it is built on manipulation rather than technical exploitation. At its foundation, phishing is a deceptive practice where attackers impersonate legitimate organizations, colleagues, or service providers to persuade individuals into disclosing sensitive information. This information may include usernames, passwords, financial credentials, or access to internal systems; all of which can be leveraged to compromise broader business operations.
Within the discipline of cybersecurity, phishing is particularly concerning because it targets the human layer of an organization’s defenses. While firewalls, endpoint protection, and intrusion detection systems have become increasingly sophisticated, phishing bypasses these mechanisms by exploiting trust. Employees, executives, and even IT personnel can be misled when a message appears authentic; especially when it mimics familiar communication patterns or urgent business requests. Industry research consistently shows human error is a contributing factor in over 70% of cybersecurity breaches, reinforcing the central role phishing plays in organizational risk.
How Phishing Works
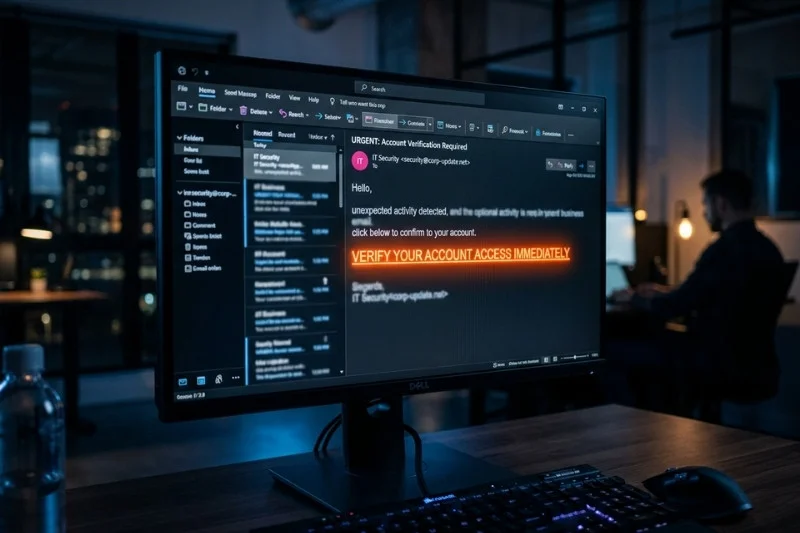
The mechanics of phishing are deceptively simple but highly effective. An attacker initiates contact through a communication channel — most commonly email — designed to resemble a legitimate message. This message often includes branding, tone, and formatting that closely mirror trusted entities, such as financial institutions, internal departments, or external vendors.
Once the recipient engages with the message, the phishing attempt progresses to its critical stage. This may involve clicking a link that leads to a fraudulent login page or downloading an attachment that installs malicious software. In cybersecurity terms, this interaction represents the breach-point, where human action enables unauthorized system access.
The true danger of phishing lies in its ability to serve as a gateway. According to multiple cybersecurity industry reports, stolen credentials are involved in a significant percentage of breaches, often enabling attackers to move laterally across networks within hours of initial access. A single compromised account can therefore escalate into a full-scale organizational incident.
Types of Phishing Attacks
Phishing has evolved into multiple forms, each tailored to increase effectiveness within different contexts. Traditional email phishing casts a wide net, targeting large groups with generic messaging. In contrast, spear phishing is highly targeted, often incorporating personal or organizational details to increase credibility and success rates.
Whaling represents a more strategic variation, focusing on senior executives whose access privileges make them particularly valuable targets. Meanwhile, smishing and vishing extend phishing beyond email into SMS and voice communications, respectively, reflecting the diversification of attack surfaces within modern cybersecurity environments.
Each variation underscores the adaptability of phishing as a threat. As communication channels evolve, so too do the methods used to exploit them, reinforcing the need for comprehensive cybersecurity awareness and layered defenses.
Business Impact of Phishing
The consequences of phishing extend far beyond the initial compromise. Financial losses can occur through fraudulent transactions or operational disruption. Global estimates suggest that phishing-related business email compromise alone has resulted in tens of billions of dollars in losses over the past decade.
Data breaches resulting from phishing may expose sensitive customer or proprietary information, leading to regulatory penalties and reputational damage. Studies indicate that the average cost of a data breach now exceeds several million dollars, with phishing frequently cited as the initial attack vector.
From a cybersecurity perspective, phishing often represents the first stage in a multi-step attack. Once access is gained, attackers may escalate privileges, move laterally across systems, and establish persistent footholds within the network. This cascading effect amplifies the impact of what may initially appear to be a minor incident.
Recent Trends in Phishing Affecting Businesses
Rise of Targeted Phishing Attacks
In recent years, phishing has shifted from broad, indiscriminate campaigns to highly targeted operations. This evolution reflects a deeper integration of data analytics and reconnaissance into phishing strategies. Attackers now gather information from social media profiles, corporate websites, and leaked databases to craft messages that resonate with specific individuals.
This level of personalization significantly increases the success rate of phishing attacks. Research shows that targeted phishing emails can have click-through rates many times higher than generic campaigns. Within cybersecurity frameworks, this trend presents a major challenge, as traditional detection systems often struggle to distinguish between legitimate communication and highly tailored phishing attempts.
Business Email Compromise and Financial Exploitation
Business email compromise has emerged as one of the most financially damaging forms of phishing. In these scenarios, attackers impersonate trusted figures such as executives or financial officers to request urgent payments or sensitive information.
The scale of this issue is substantial. Global law enforcement agencies have reported that BEC scams account for billions of dollars in annual losses, making them one of the costliest forms of cybercrime. The effectiveness of these attacks lies in their alignment with real business processes, making them difficult to detect through conventional cybersecurity controls.
Expansion into Multi-Channel Phishing
Phishing is no longer confined to email. As businesses adopt diverse communication platforms, attackers have expanded their reach to include messaging applications, SMS, and voice calls. This multi-channel approach increases the likelihood of success, as it allows phishing attempts to intersect with employees across different contexts.
Recent data indicates a sharp increase in smishing, and mobile-based phishing attacks, reflecting the growing reliance on mobile devices in business operations. For cybersecurity professionals, this trend necessitates a broader defensive strategy that extends beyond traditional email filtering.
Artificial Intelligence and Automation
The integration of artificial intelligence into phishing campaigns has further increased their sophistication. Attackers can now generate highly convincing messages at scale, mimic writing styles, and even create realistic audio or video impersonations.
This technological advancement has significantly altered the cybersecurity landscape. AI-generated phishing emails have been shown to outperform traditional phishing in both realism and effectiveness, placing additional pressure on defensive systems.
Remote Work and Decentralized Risk
The rise of remote work has introduced new vulnerabilities into organizational cybersecurity. Employees operating outside secure office environments often rely on personal networks, and devices, which may lack robust protections.
Studies conducted since the global shift to remote work indicate a notable increase in phishing attempts targeting remote employees. This decentralization creates additional entry points for attackers and requires businesses to rethink their cybersecurity strategies.
Common Phishing Practices Used by Attackers
Email Spoofing, and Identity Deception
One of the most prevalent phishing techniques involves email spoofing: where attackers manipulate sender information to appear as though the message originates from a trusted source. This tactic exploits the inherent trust users place in familiar names, and domains.
Additionally, the sophistication of spoofing has increased significantly: with attackers replicating entire communication threads and corporate branding. This level of detail makes phishing attempts more convincing and harder to detect within cybersecurity systems.
Credential Harvesting Through Fake Interfaces
A central component of many phishing campaigns is the use of fraudulent websites designed to capture user credentials. These sites often replicate legitimate login pages with remarkable accuracy.
Cybersecurity data shows that credential harvesting remains one of the most successful phishing techniques, as users frequently fail to notice subtle differences in URLs or site design. Once credentials are obtained, attackers can gain immediate access to sensitive systems.
Malware Delivery via Attachments
Phishing emails frequently include attachments that appear benign but contain malicious code. When opened, these files can install malware, granting attackers control over the affected system.
This method is particularly dangerous because it can lead to ransomware attacks, which have increased dramatically in recent years. Many ransomware incidents originate from phishing emails, highlighting the intersection between social engineering and technical cybersecurity threats.
Psychological Manipulation, and Behavioral Exploitation
At the core of phishing lies psychological manipulation. Attackers craft messages that evoke urgency, fear, or curiosity, prompting recipients to act without careful consideration.
Behavioral studies in cybersecurity have shown that urgency-based messaging significantly increases the likelihood of user interaction. This human factor remains one of the weakest points in organizational cybersecurity defenses.
AlphaKOR as a Cybersecurity Solution Provider
Integrated Cybersecurity Approach
For businesses seeking to mitigate phishing risks effectively, partnering with an experienced provider such as AlphaKOR can play a decisive role. AlphaKOR positions itself as a comprehensive IT and cybersecurity partner, delivering solutions that extend beyond isolated tools, to encompass the full operational environment of an organization.
Their approach to cybersecurity reflects an understanding that phishing is rarely an isolated event. Instead, it is often the entry point into broader system compromise. As such, AlphaKOR emphasizes layered security strategies designed to detect, contain, and respond to threats at multiple levels.
Security Operations and Continuous Monitoring
A defining aspect of AlphaKOR’s cybersecurity offering is its emphasis on continuous monitoring through a dedicated Security Operations Centre. This capability enables real-time visibility into network activity, allowing potential phishing threats to be identified before they escalate into more serious incidents.
Organizations with 24/7 monitoring capabilities have been shown to reduce breach detection times significantly, which is critical in limiting the impact of phishing-related incidents.
User-Focused Protection and Risk Reduction
Recognizing that phishing targets individuals, AlphaKOR integrates user-focused protections into its cybersecurity strategy. This includes the implementation of multi-factor authentication (MFA), secure access controls, and ongoing user awareness initiatives.
Research consistently demonstrates that MFA can prevent the vast majority of credential-based attacks, making it one of the most effective defenses against phishing.
Endpoint Security and Incident Response
AlphaKOR also provides advanced endpoint detection and response capabilities, ensuring that devices across the organization are continuously monitored for signs of compromise. In the event phishing leads to unauthorized access, these systems enable rapid containment and remediation.
Effective incident response can reduce the overall cost of a cybersecurity breach by a substantial margin, highlighting the importance of preparedness.
Business Continuity and Long-Term Resilience
Beyond immediate threat mitigation, AlphaKOR supports long-term resilience through backup solutions and business continuity planning. These measures ensure that even if phishing results in system disruption, organizations can recover quickly and maintain operational stability.
Their experience working with businesses across various industries, particularly within the Windsor region, positions them as a practical and accessible partner for organizations seeking to strengthen their cybersecurity posture.
Conclusion
Phishing continues to represent one of the most significant challenges in cybersecurity, affecting organizations regardless of size or industry. Its effectiveness lies in its simplicity and adaptability, exploiting human behavior while evolving alongside technological advancements.
To address this threat, businesses must adopt a comprehensive approach that combines awareness, technology, and strategic partnerships. By understanding how phishing operates, recognizing emerging trends, and implementing robust cybersecurity measures, organizations can significantly reduce their exposure.
Equally important is the role of experienced providers such as AlphaKOR, whose integrated cybersecurity solutions offer both protection, and resilience. In an environment where phishing remains a constant threat, proactive defense is not merely advisable: it is essential for long-term success.

